ACCESSORIES FOR THE PARANOID
Katja Trinkwalder and Pia-Marie Stute have designed Accessories For The Paranoid, a series of add-on accessories for those who are concerned about surveillance and their data security.
The project explores an alternative approach to data security through four different “parasitic” objects, such as a webcam that projects fabricated scenes and a button that generates fake online data. These pieces work to block or thwart the collection of people’s user information in different ways by generating fake data to blur their digital profiles, hiding users’ true data identities behind “a veil of fictive information”.
v
The first object in the series is the “un-hacking” webcam, which takes the principle of a toy camera and applies it to data security by displaying different, fabricated scenes through the webcam as if it was in real-time. The webcam addresses fears of hackers gaining access to the cameras positioned at the top of users’ laptops or smart devices, allowing them to see into their personal spaces.
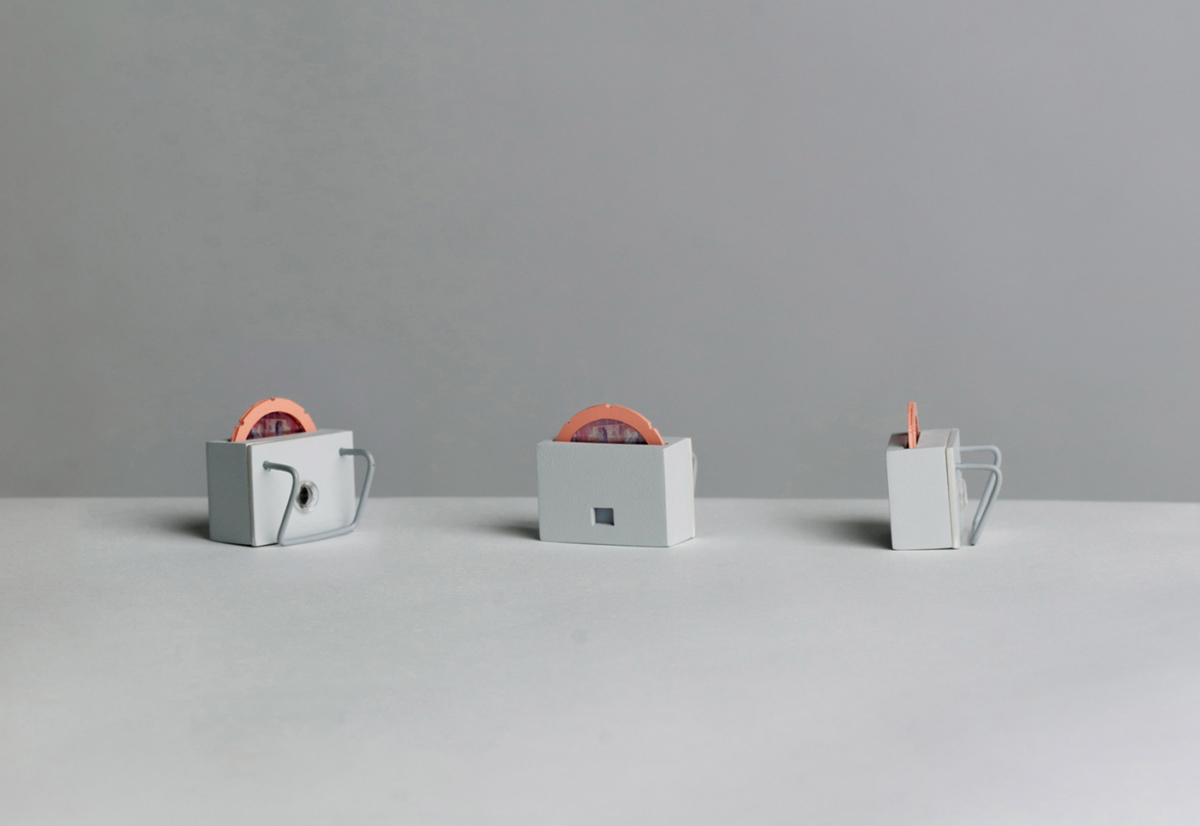
The second object is an add-on to the well-known Amazon Echo virtual assistant, which responds to the call of “Alexa”. The design aims to prevent the user’s sensitive information from being heard either by fitting onto the top of the device and “numbing” Alexa when needed, or by feeding fake information to the device. For the latter, users can choose between three modes to play over the voiceover. These are white noise that lets no information slip through, pre-recorded quests to occupy Alexa with useless tasks, or dialogues from random movie scenes that make the device collect fake information about the user and their surroundings.
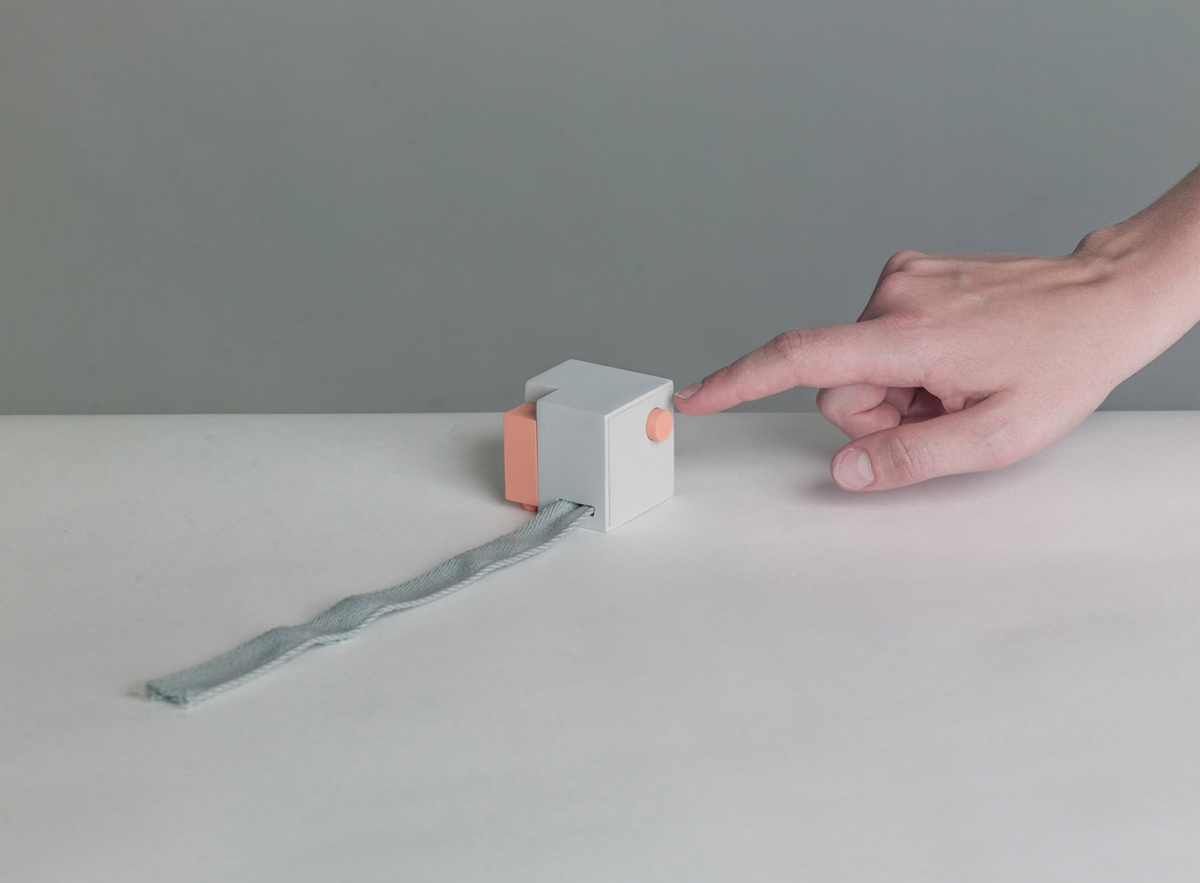
Connected to any computer, the third object in the series will generate fake online data. By pushing the button, an algorithm will randomly create site-specific content on the websites of services such as Google, Facebook, YouTube, Twitter or Amazon. Once the browser has been opened, this object will access a popular service and leave fault digital traces.
The final object in the collection can be connected to any device able to collect data. It aims to blur people’s use patterns by randomly pushing the buttons of the device it’s attached to when activated. This then creates fake user patterns when the user sleeps during night time, or when they’re not at home.
While none of these prototype products can be bought, they act as a demonstration of the common desire to protect our privacy.
v
All Rights reserved to Katja Trinkwalder and Pia-Marie Stute
via dezeen